
China MNO Core Network Solution: Powering Next-Generation Telecom Infrastructure
2026-05-10
As China's mobile network operators race toward 5G-Advanced and beyond, the core network has never been more pivotal. It’s the invisible engine behind every ultra-reliable low-latency connection, every massive IoT deployment, and every seamless slice of network intelligence. But building a future-proof core that balances performance, scalability, and cost is a monumental challenge. This is where IPLOOK’s innovative core network solutions step in—purpose-built to simplify complexity and accelerate service agility. In this blog, we explore how IPLOOK empowers MNOs with cloud-native, converged, and fully compliant infrastructure, ready to ignite the next wave of digital transformation.
A Cloud-First Foundation for Next-Generation Services
Building modern services on a cloud-first foundation means more than just moving workloads to virtual machines. It reshapes how infrastructure is designed, starting with event-driven architectures and serverless compute models that scale precisely with demand. Instead of forecasting capacity months ahead, teams deploy granular functions that execute in milliseconds and vanish just as quickly. This eliminates idle resource costs and drastically reduces operational overhead, allowing engineers to focus on the code that differentiates the business rather than the plumbing that keeps it running.
A fundamental shift also occurs in data management and integration. Cloud-native databases with automatic replication, point-in-time recovery, and multi-region support replace rigid monolithic stores. APIs become the primary connective tissue, enabling real-time data flows between services without brittle point-to-point integrations. Security evolves as well, moving from perimeter-based defenses to zero-trust models where every request is authenticated and authorized at the service mesh layer. This posture allows organizations to safely expose capabilities to partners and end users, creating ecosystems that monetize data and functionality in entirely new ways.
Perhaps the most transformative aspect is how rapidly teams can experiment and adopt emerging technologies. With a cloud-first foundation, integrating AI inference, IoT stream processing, or blockchain-based verification becomes a matter of configuration rather than a multi-year infrastructure project. Developers weave in pre-built services for identity, messaging, and analytics through standard interfaces, turning months of backend work into days of frontend iteration. The result is a platform that doesn’t just serve today’s needs but continually absorbs technological advances, keeping the organization perpetually ready for what comes next.
Scalability Without Compromise: Handling the Data Tsunami
Growth brings a peculiar challenge: the tools and architectures that comfortably handled yesterday’s workloads can buckle under the relentless pressure of today’s data volumes. The real test isn’t just adding more servers or spinning up extra instances—it’s doing so without letting latency creep up, consistency slip, or operational complexity spiral out of control. Many platforms claim to scale, but few manage to maintain the crisp responsiveness and data integrity that teams rely on when the floodgates open.
What separates genuinely scalable systems from the also-rans is how they approach the problem. Instead of bolting on capacity as an afterthought, the foundation is built around distributed, cooperative primitives that spread workloads naturally. Queues, streams, and stateful processing units choreograph their work so that adding capacity actually feels like a seamless extension, not a fragile patch. This means a sudden tenfold spike in event ingestion doesn’t trigger a cascade of timeouts or dropped messages—the system absorbs the surge, redistributes the load, and keeps humming along, with latency graphs staying stubbornly flat.
Of course, the human side matters just as much. Engineers don’t want to babysit auto-scaling groups or decode cryptic backpressure errors at 3 a.m. Real scalability means the operational burden stays low even as the infrastructure footprint grows. That requires thoughtful observability, intelligent defaults that can be overridden but rarely need to be, and an architecture that handles the messy realities of partitioning, replication, and failover without exposing that complexity to the people building on top of it. When the data tsunami hits, the only thing teams should notice is that everything still works—quietly, predictably, and without compromise.
Intelligent Operations: Beyond Manual Network Management
Networks have grown too complex and dynamic for traditional, hands-on approaches. Intelligent operations weave together automation, real-time telemetry, and contextual analytics to replace reactive firefighting with proactive precision. Instead of manually tracing issues through scattered dashboards, teams rely on platforms that learn normal behavior, surface anomalies, and often resolve them before users notice—turning raw data into actionable awareness without constant human oversight.
The shift goes beyond simple scripted tasks; it’s about systems that adapt. When a device misbehaves, the environment can self-heal by rerouting traffic, adjusting configurations, or rolling back changes based on historical success patterns. This isn’t just about speed—it’s about offloading repetitive decisions, freeing engineers to focus on architecture and innovation rather than midnight alerts. The result is a network that feels less like a fragile collection of boxes and more like a living ecosystem capable of managing its own health.
Adopting this mindset demands a cultural change that bridges the gap between network veterans and tooling. Processes once guarded as “tribal knowledge” become encoded in models that guide continuous improvement, while trust grows through transparency and gradual autonomy. The goal isn’t to remove human judgment but to elevate it—letting intuition and experience drive strategy while machines handle the predictable noise, ultimately making every operator more effective.
Fortifying the Core: Security in an Interconnected World
Digital connectivity has woven itself into every strand of modern life, from power grids to personal devices, creating a vast web of interdependencies. Each new connection, however, introduces a potential entry point for threats that can ripple across systems in seconds. The challenge isn't just about defending perimeters anymore; it's about rethinking the entire architecture of trust, ensuring that the foundational layers of our digital society can withstand both targeted attacks and quiet systemic failures.
True resilience starts with invisible, often overlooked building blocks—firmware integrity, cryptographic agility, and the assumption that no component is inherently safe. By embedding verification mechanisms at the silicon level and enabling systems to adapt their defenses in real time, we create a living immune system rather than a static wall. This shift demands collaboration across industries that historically operated in isolation, forcing hardware manufacturers, cloud providers, and software developers to align on a common security language.
Perhaps the most profound change lies in how we perceive failure itself. In an interconnected ecosystem, containing the blast radius of a breach matters as much as preventing one. Designs that prioritize graceful degradation, where compromised segments are isolated without collapsing entire networks, turn security from an absolute state into a dynamic negotiation. This mindset transforms core infrastructure into something that doesn't just resist harm but actively learns, heals, and grows stronger under pressure.
Unifying the Ecosystem: Multi-Vendor Interoperability in Practice
Truly unified ecosystems don’t happen by accident—they emerge when vendors commit to aligning their technologies around shared operational realities rather than theoretical standards. In practice, this means moving beyond basic API compatibility toward deep integration of monitoring frameworks, security protocols, and data exchange formats that work seamlessly across different hardware and software stacks. When a network operations team can apply a single set of automation rules to devices from three different manufacturers without rewriting scripts, you know the interoperability promise is being delivered, not just advertised.
The real challenge isn’t technical on paper—it’s behavioral. Engineering teams often become fluent in their primary vendor’s ecosystem, creating an unconscious bias that bleeds into architecture decisions. Breaking that pattern requires deliberate exposure to multi-vendor lab environments where teams troubleshoot real failures that span across boundaries. One surprisingly effective approach has been rotating vendor-specific engineers through cross-functional integration sprints, forcing them to experience the pain points of their counterparts firsthand. That shared discomfort often sparks more innovation than any standard body whitepaper.
We’ve moved past the era where “interoperability” meant simply exchanging data packets without error. Today’s practice involves joint lifecycle management: synchronized firmware upgrades, unified telemetry pipelines that feed into a single analytics engine, and security policies that maintain their integrity end-to-end regardless of the underlying platform. The vendors who understand this aren’t just checking boxes on an RFP—they’re actively participating in customer operations, learning where the friction truly lives and engineering it away collaboratively. The result feels less like a collection of certified parts and more like a coherent system that just happens to have different brand labels on the chassis.
Tailoring the Core to China’s Digital Ambitions
Building a technology foundation that aligns with China’s digital trajectory demands more than simply localizing existing platforms. It involves recrafting the underlying architecture to leverage domestic innovations in AI, cloud computing, and data processing, while ensuring interoperability within China’s unique internet ecosystem. This often means replacing global components with homegrown alternatives that not only meet performance benchmarks but also reflect the design philosophies prevalent in the country’s tech sector.
The true challenge lies in balancing global scalability with local depth. Companies must integrate China’s rapid iteration culture into their core processes, adopting agile methodologies that resonate with local engineering teams. This shift often leads to building modular systems that can quickly adapt to changing regulations, consumer behaviors, and partner networks, turning compliance from a constraint into a catalyst for innovation.
Beyond technology, tailoring the core means embracing the market’s distinct value creation models. From super-app ecosystems to industrial internet platforms, success hinges on embedding the core into China’s collaborative digital fabric. It calls for rewiring internal R&D priorities to co-create with local stakeholders, ensuring that the resulting capabilities are not imported solutions, but ones genuinely born from and for China’s ambitious digital landscape.
FAQ
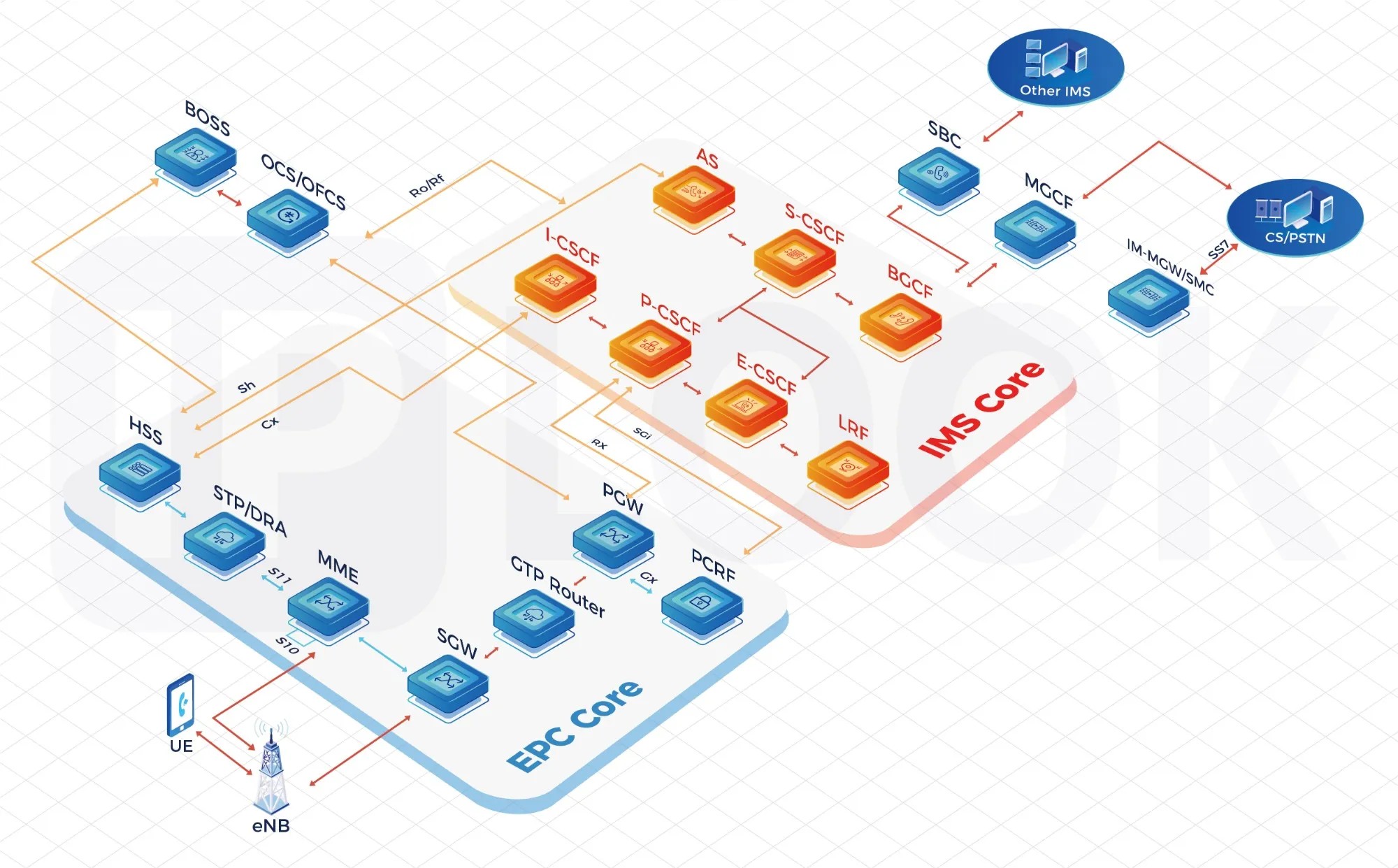
It provides a containerized, cloud-native core that unifies 4G, 5G, and future network functions on a single platform. This enables operators to launch services faster, reduce hardware dependency, and simplify multi-generational network management—critical for a market with over a billion subscribers.
The architecture is built with AI-native orchestration and intrinsic support for network slicing and ultra-low latency. It allows operators to dynamically allocate resources for emerging use cases such as holographic communication, massive IoT, and real-time industrial control without forklift upgrades.
Unlike legacy monolithic cores, this solution decouples software from hardware and uses microservices. This means network functions can be updated independently, scaling is granular, and service continuity is maintained even during upgrades—key for minimizing downtime in high-density urban environments.
Yes, it’s engineered for hyperscale with stateless design and intelligent load distribution. It can handle hundreds of millions of simultaneous connections while maintaining consistent performance, which is essential during events like Spring Festival travel rush when signaling surges abruptly.
The solution enforces strict data localization and encryption by design, aligning with China’s cybersecurity laws. It includes built-in security functions such as a dedicated firewall element, real-time threat detection, and lawful interception points without compromising latency or throughput.
Automation is central—both for lifecycle management and real-time optimization. The platform uses intent-based policies and closed-loop analytics to self-heal, auto-scale, and predict traffic patterns, cutting manual intervention drastically and letting engineering teams focus on service innovation rather than maintenance.
It supports a phased migration approach with interworking gateways that bridge legacy EPC and the new 5G core. Operators can migrate user groups or services gradually, avoiding big-bang cutovers, and reuse existing infrastructure investments while gaining cloud-native agility.
Conclusion
China's mobile network operators are reshaping their core infrastructure to meet soaring demands, blending cloud-native agility with uncompromising scalability. By adopting a cloud-first architecture, operators can rapidly launch next-generation services while gracefully absorbing massive data surges from 5G and IoT. This transformation hinges on intelligent operations, where AI-driven automation replaces manual oversight, enabling predictive maintenance and self-healing networks that reduce outages and operational costs.
In an era of heightened cyber threats and complex multi-vendor environments, the solution embeds robust security frameworks directly into the core, safeguarding data integrity across every interconnection point. It fosters true interoperability, seamlessly integrating equipment from diverse suppliers without sacrificing performance. Ultimately, this approach is tailored to China's digital ambitions, aligning with national strategies like Digital China and the Belt and Road Initiative, ensuring that the core network becomes a resilient, efficient, and future-ready foundation for the country's digital economy.
Contact Us
Contact Person: Shimmy
Email: [email protected]
Tel/WhatsApp: 85253392231
Website: https://www.iplook.com

